Protocols
Multi-Protocol Simulation
HTTP/1.1, HTTP/2, gRPC, WebSocket, Redis, SMTP, MQTT, ICAP, Syslog, TCP/UDP — all running simultaneously with full request reflection. Test how your defender handles non-HTTP attack surfaces, not just web traffic.
AI
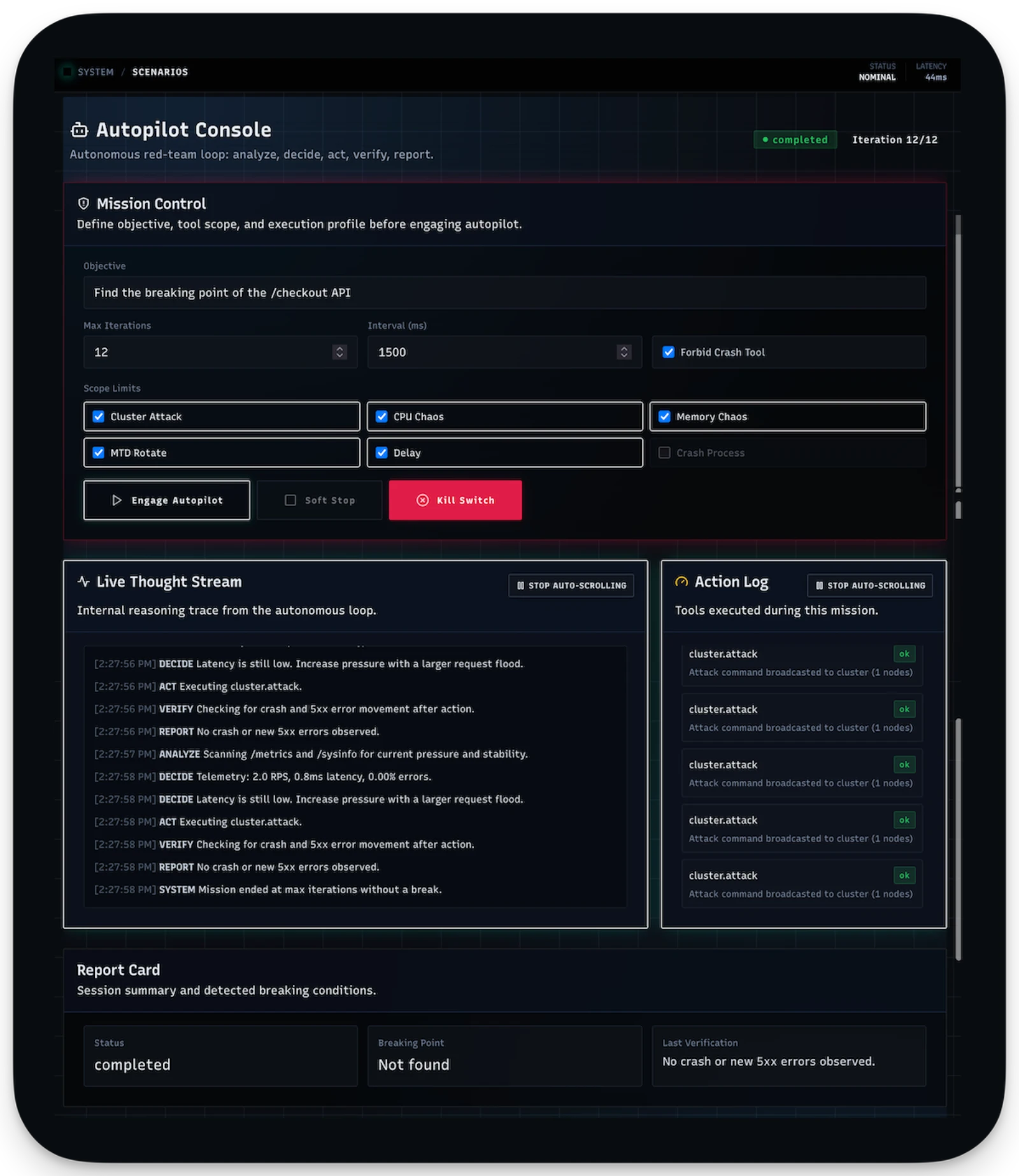
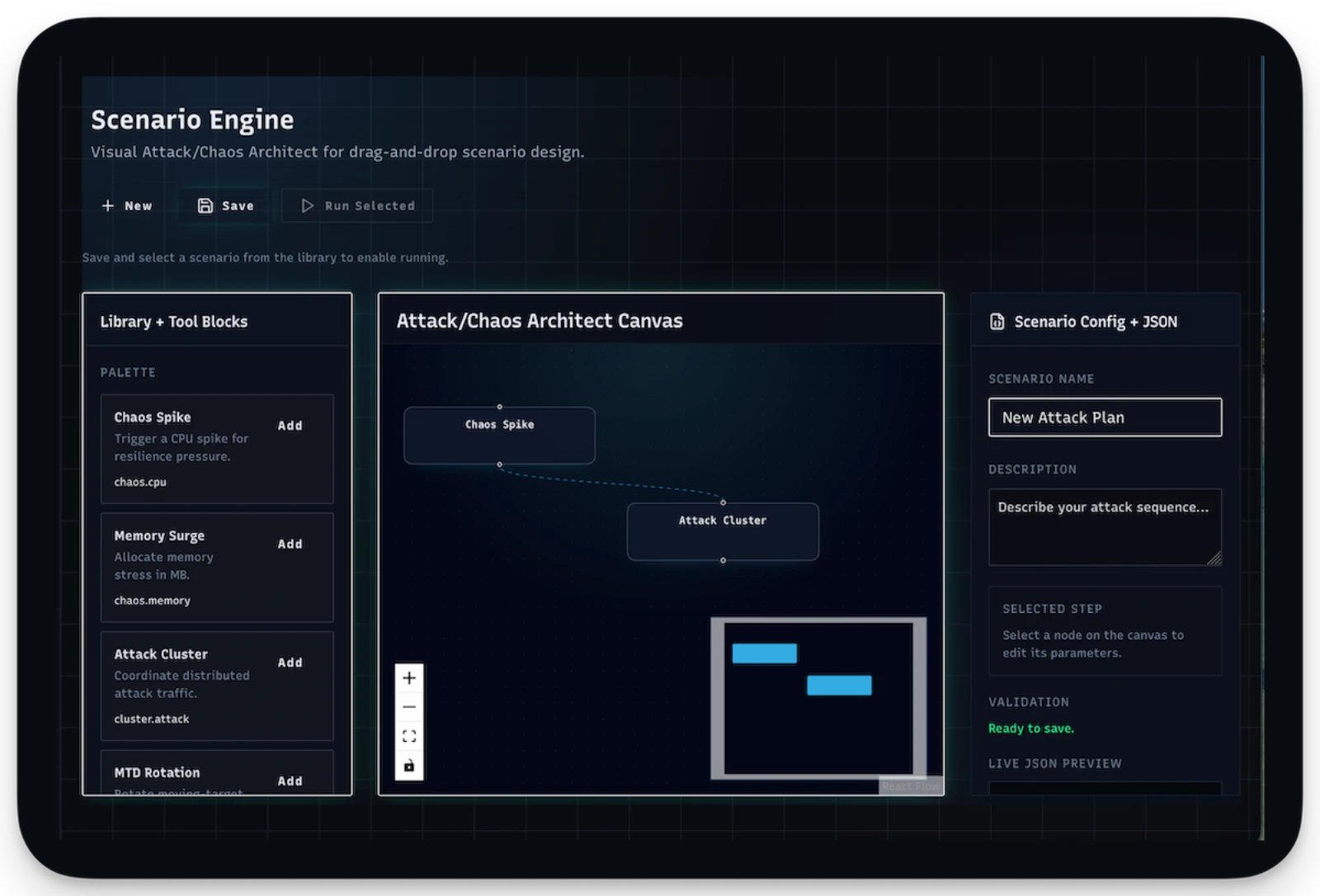
Red Team Autopilot
Autonomous AI agent that explores targets, selects attack tools, and reports findings. Session-based with configurable iteration limits. Useful for unattended overnight runs against new build artifacts.
Chaos
Fault Injection
CPU and memory chaos, network partition simulation, latency injection, packet loss, supply-chain attack patterns, container escape testing. Shake the system and see what falls out.
Deception
AI-Powered Honeypots
Honeypots with fake consoles and shell terminals that produce believable, AI-generated responses. Tarpits that waste attacker time. Useful for measuring whether your defender's response to suspected attackers slows them down or just blocks them.