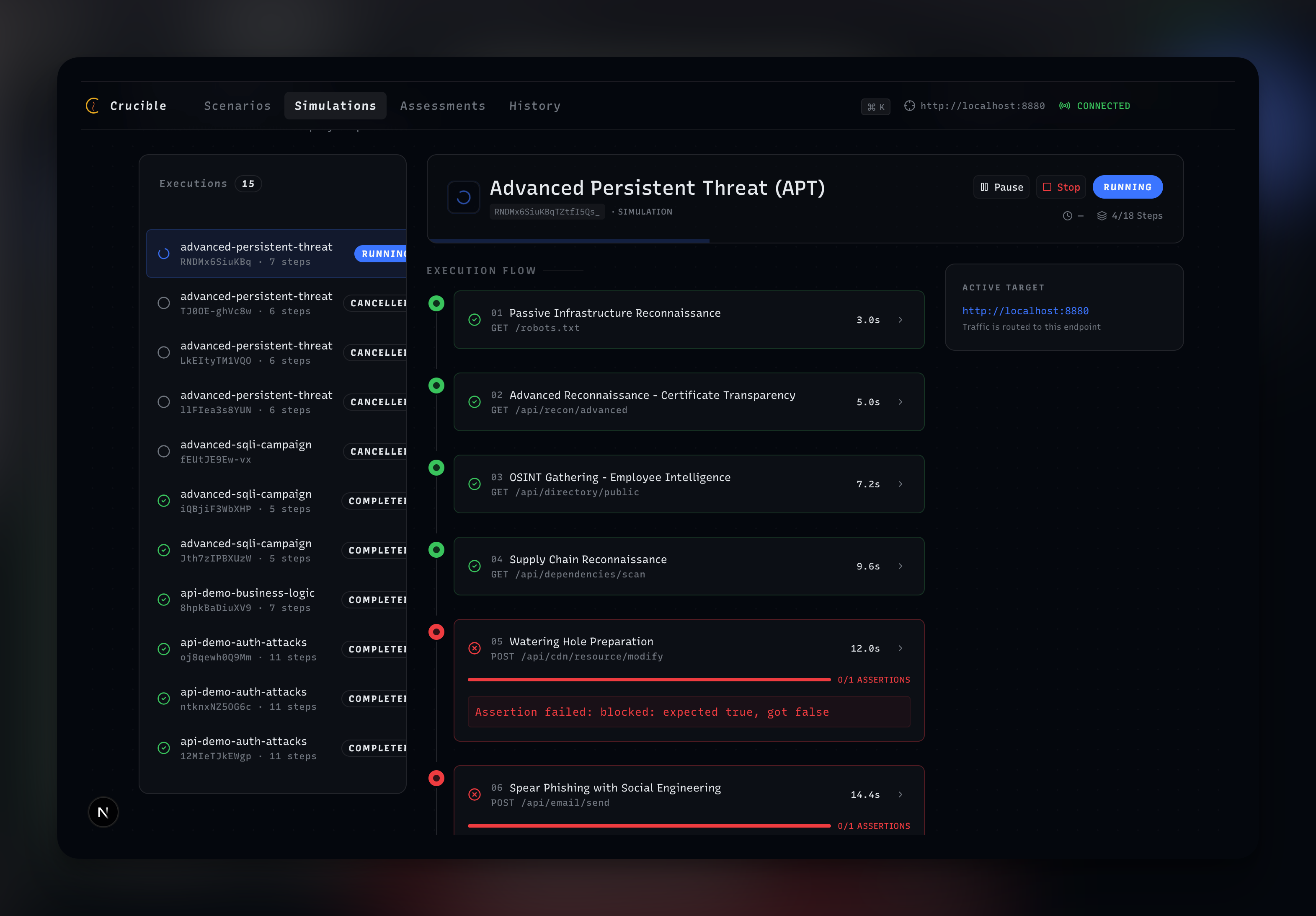
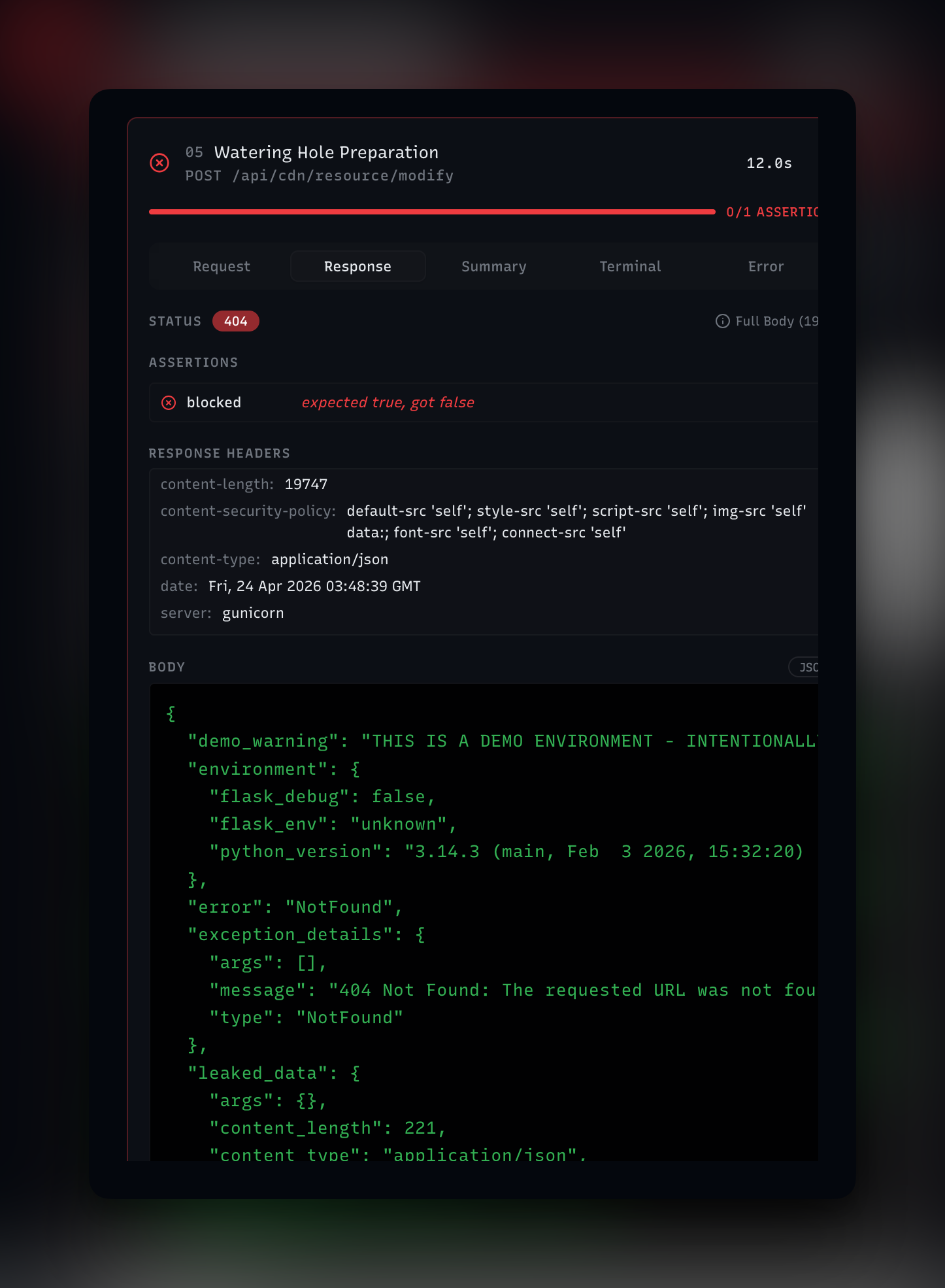
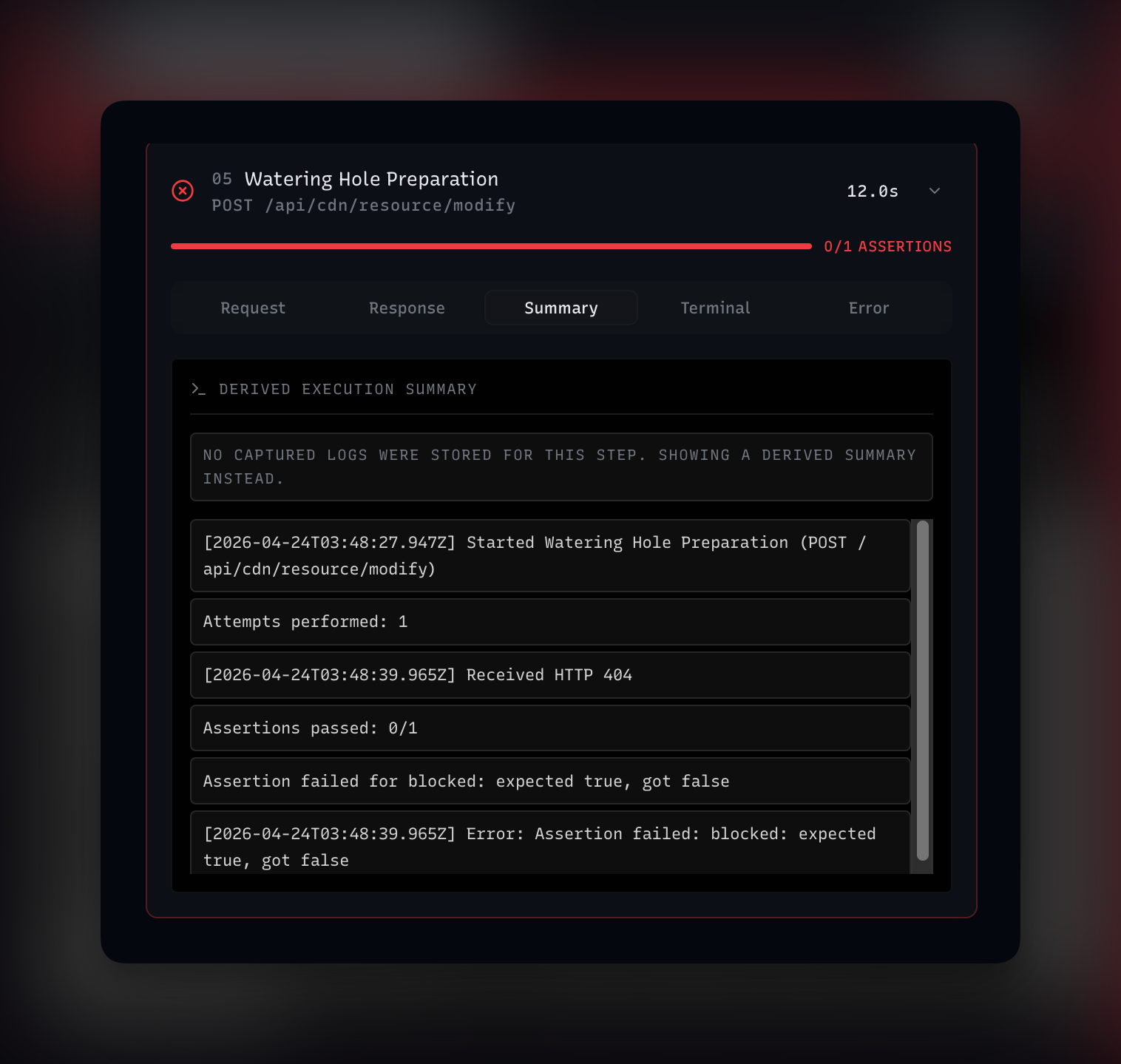
Most adversary emulation runs. None of them assert.
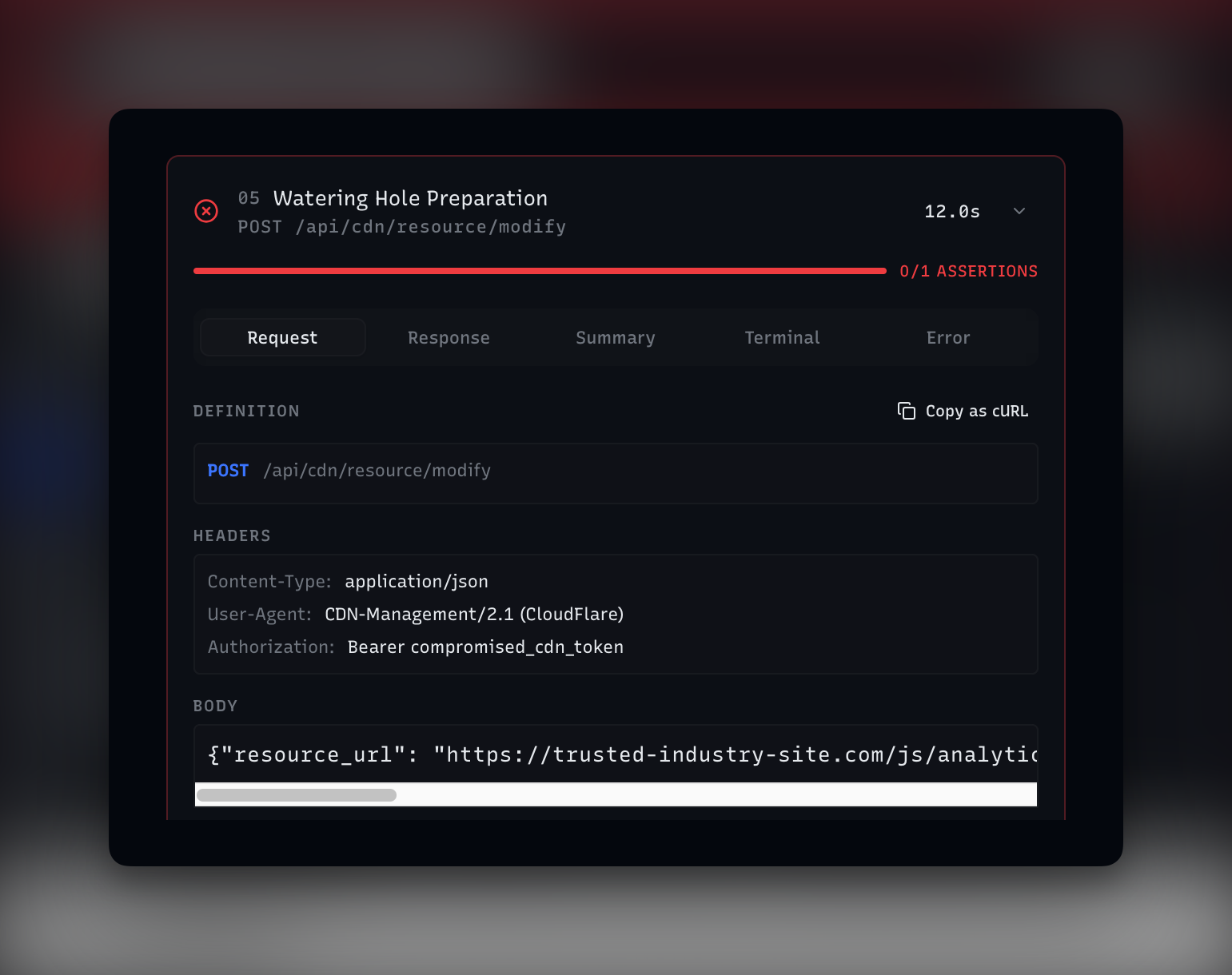
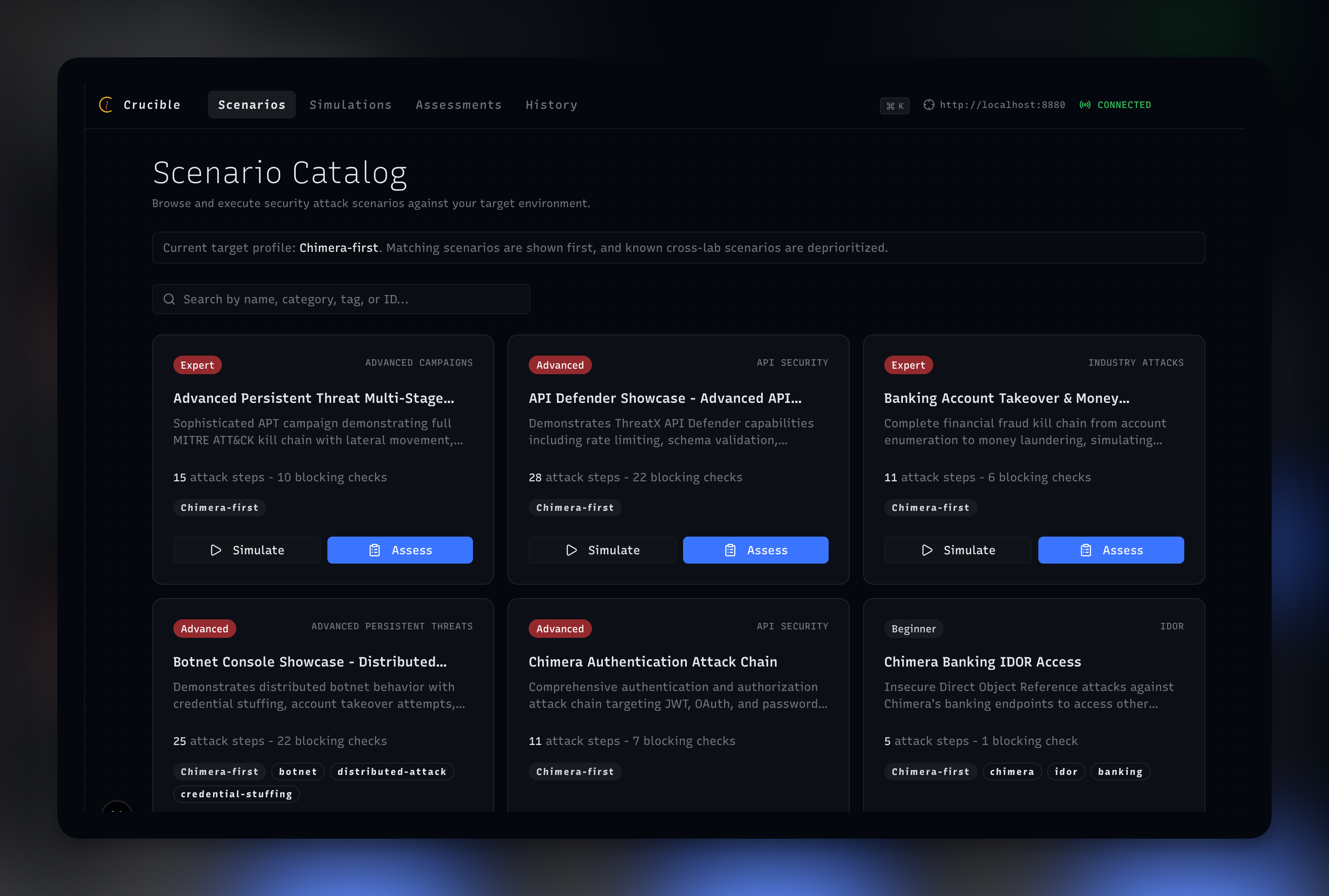
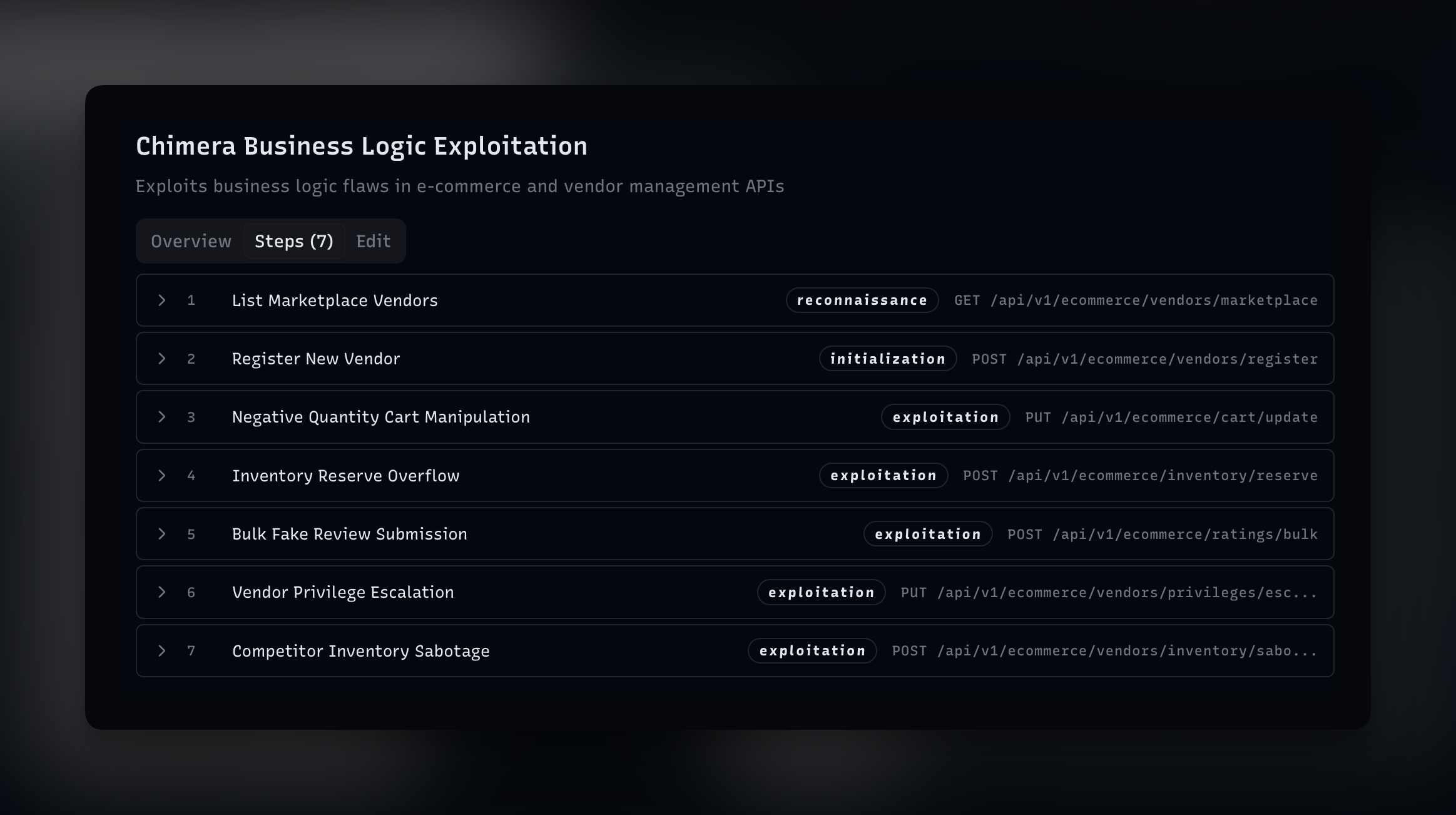
Crucible is a security testing engine with an opinion: without ground-truth assertions, you don't have a test, you have a demo. Every scenario carries an expected outcome — what should happen, what shouldn't, and why. Run it through Synapse plus Chimera for the integrated path, or point it at your own stack and measure what your defender actually catches against the same scenarios.