Learn
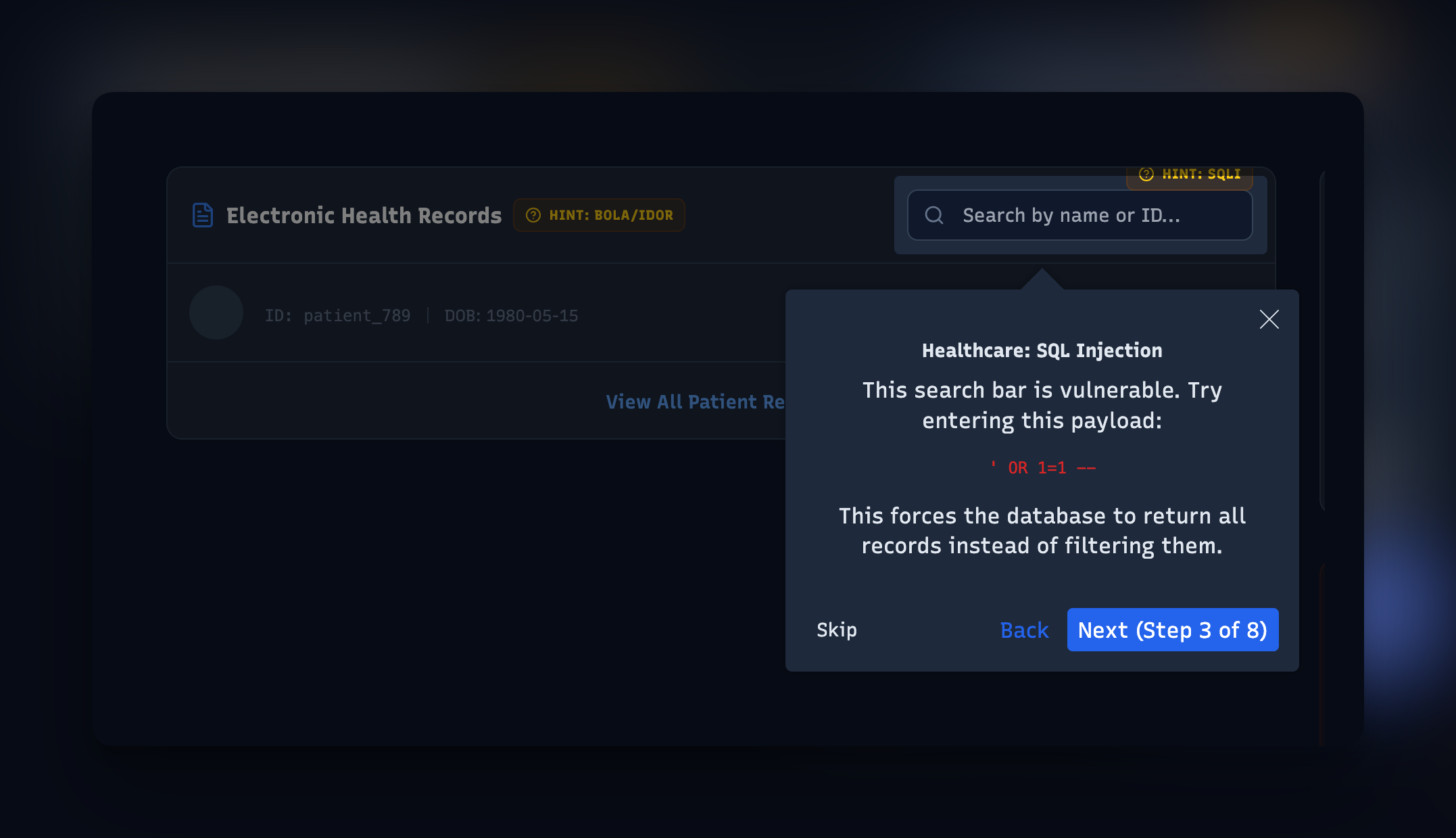
Exploit Tours
Step-by-step guided walkthroughs of complete exploit chains. Follow along as attacks unfold across realistic multi-step scenarios — recon, exploit, escalate, exfil — with the full chain demonstrated against real endpoints.
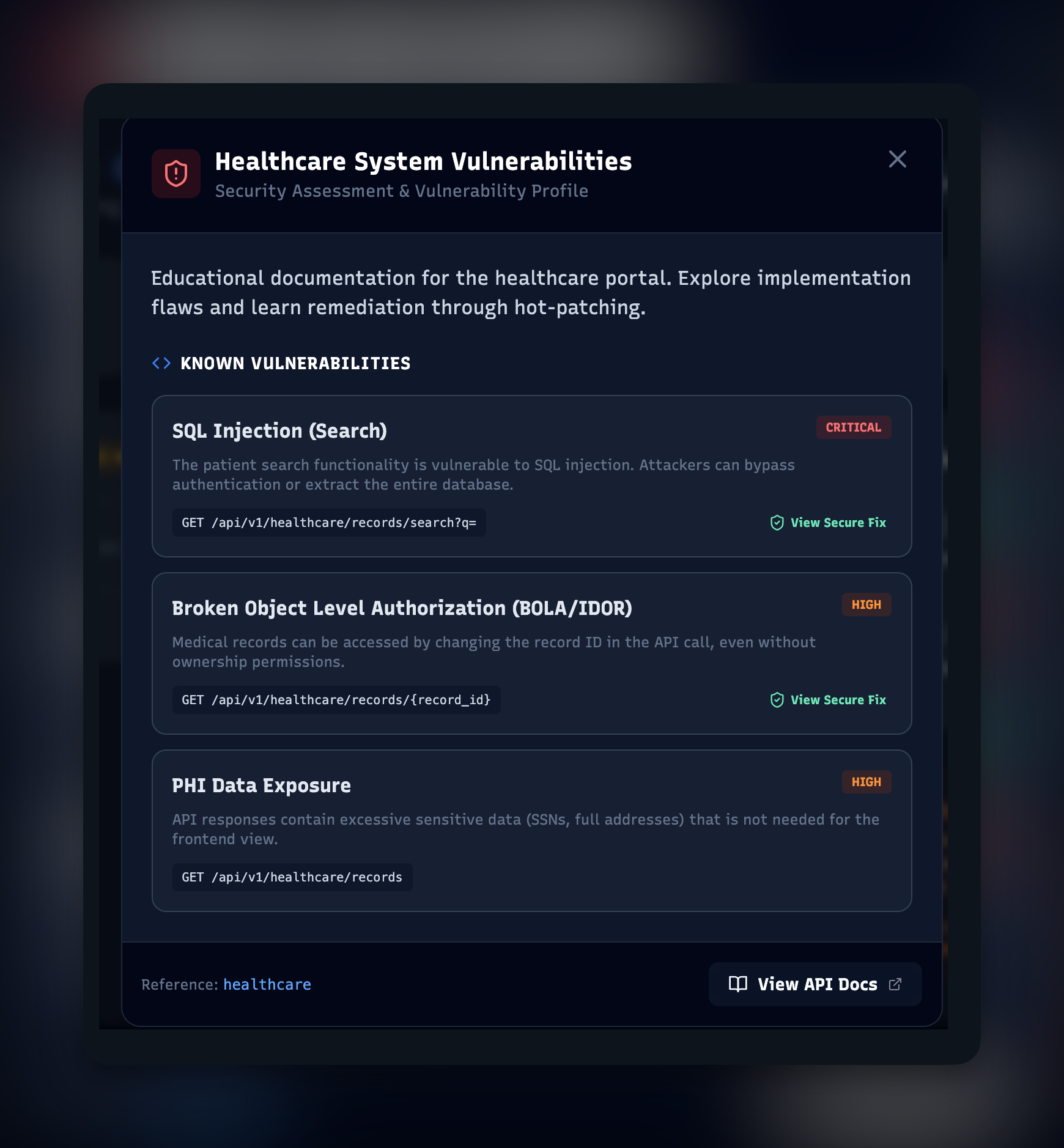
Inspect
X-Ray Inspector
See exactly where vulnerabilities exist in the source and how to remediate them. Connects every attack surface to the line of code that introduced it, with actionable fixes attached. The "why" behind every flaw.
Defend
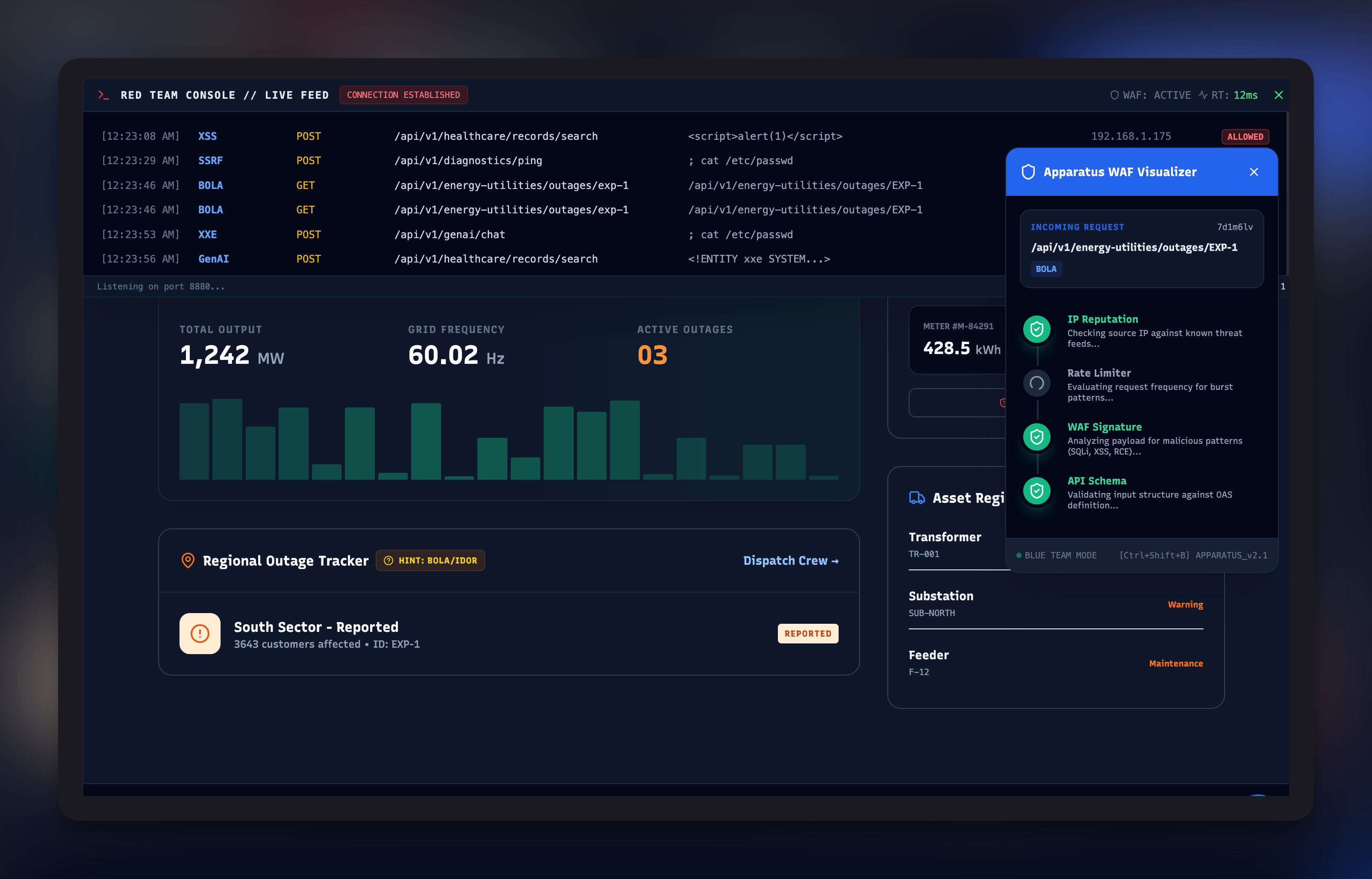
WAF Visualization
Blue-team mode integrates with Synapse to show attack flows as they hit the defender. Watch detection cycles run, see which rules catch what, debug WAF policy in real time against real attack traffic.
AI
LLM Kill Chain
Track and visualize exploit chains targeting LLMs. Prompt injection, jailbreaking, indirect injection, data exfiltration through tool calls — mapped to attack stages and tied to remediation patterns.